IT Guides and Resources for Small Businesses
Practical IT guides explaining how technology problems and security risks occur across websites, email systems, cloud services, devices, and local networks used by organisations, professionals, and individuals.
These guides focus on how systems normally behave, why certain problems occur, and what realistic steps help restore stability or reduce risk.
Some issues appear to affect one device but are actually linked to shared systems such as email platforms, cloud services, DNS, website configuration, or network infrastructure. Where that happens, structured IT support may be required rather than isolated troubleshooting.
Explore how structured IT support and infrastructure services help maintain business-critical systems across London, Hertfordshire and Essex.
Our guides explain common IT problems in plain language.
If you are reviewing support options in a specific area or exploring the broader services we provide, you can view the towns we cover and our full services framework below.
Local IT Support for Businesses Across London, Hertfordshire and Essex
Browse guides by topic
This page groups our guides by topic so readers can move more quickly to the areas most relevant to their question or concern. Use the links below to jump to each guide section.
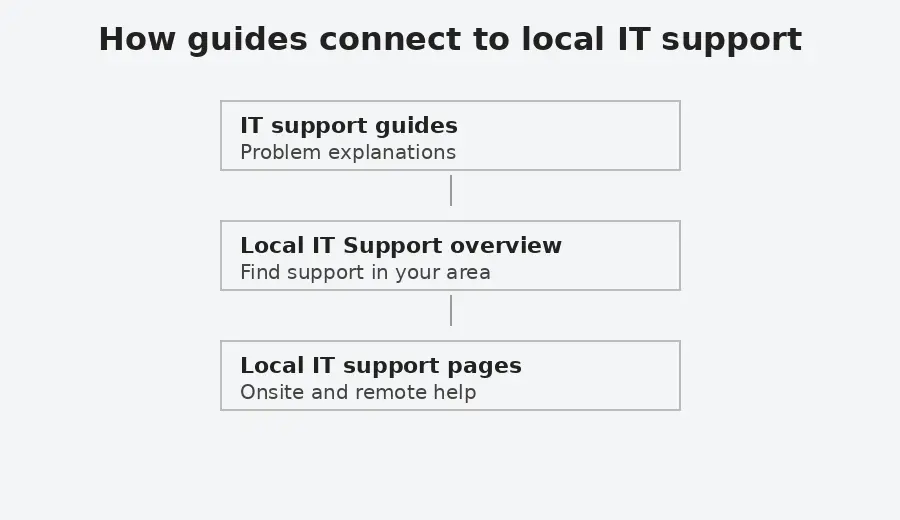
This diagram shows how practical IT issues can connect to local support and, where necessary, to broader IT support for shared business systems.
When a Guide Becomes a Wider IT Issue
Many technical issues begin with a single symptom but may relate to wider configuration, authentication, network or infrastructure dependencies.
When this happens, it can indicate that responsibility extends beyond one device and into shared systems that require ongoing oversight.
Understanding the types of IT issues covered in these guides
The guides below are grouped into several areas that reflect common types of technology issues encountered when supporting organisations, professionals, and individuals. These areas include email systems, website platforms, network connectivity, security risks, and data protection.
Grouping the guides in this way makes it easier to explore related topics and understand how different technical systems interact. Many issues that appear to affect a single device may actually involve wider infrastructure such as email authentication systems, cloud services, DNS configuration, or network connectivity.
Security, Infrastructure and Online Accounts
Guides explaining core security concepts, managed browser controls, internet infrastructure, account protection, backup, and layered security in practice.
Guides:
What is layered security and why does it matter
Explains what layered security means and why modern technology depends on multiple overlapping controls. Covers websites, devices, networks, browsers, accounts, backups, and third party services.
How do cyber attacks usually start in small businesses?
Explains common ways cyber attacks begin in small business environments, including phishing, weak accounts, exposed services, supplier access and misleading support routes. Outlines why layered security, monitoring and recovery planning need to work together rather than relying on one control.
Can smart devices be a security risk?
Explains how smart devices and ordinary network connected equipment can create security risks when they are unsupported, poorly configured, or connected to sensitive systems. Covers routers, cameras, printers, smart TVs, thermostats, NAS devices and similar equipment, with practical steps for reducing exposure.
Can Microsoft Defender flaws put Windows devices at risk?
A sensible starting point is to keep Microsoft Defender active, keep Windows devices fully patched, and review whether surrounding controls are strong enough to support it when one weakness appears.
Should PowerShell execution policy be Unrestricted on the whole machine?
Explains what PowerShell execution policy does, why setting Unrestricted across the whole machine is often too broad, and how to interpret common results in plain language. Also outlines what settings such as RemoteSigned do and do not tell you, so the topic is understood as part of wider security rather than as a single hardening step.
How to improve browser security in Chrome and other browsers
Explains how browser security and privacy settings work in Chrome and other browsers, including permissions, extensions, Secure DNS, browser fingerprinting, and cookies. Also outlines what these controls can reduce, what they do not prevent, and how to review browser exposure more carefully.
Why won’t Chrome ADMX templates import into Intune?
Explains why Chrome ADMX template imports can fail in Microsoft Intune, including missing Windows or Google template dependencies and namespace errors. Covers the correct import order for Windows, Google and Chrome templates, language file checks, and how the issue fits into managed browser policy.
What is NextDNS and what does it do?
Explains what NextDNS is, what it does, how DNS filtering works, what it can help block, and where its limits are. Also outlines how it differs from broader platforms such as Cloudflare and where it fits in layered security.
Why DNSSEC matters and how DNS attacks can redirect internet traffic
Explains how the Domain Name System (DNS) directs internet traffic and why attackers sometimes attempt to manipulate DNS responses. The guide outlines how DNS poisoning and related attacks can redirect users to fraudulent systems and how DNSSEC introduces cryptographic verification to help ensure DNS answers are authentic.
Email validation and security explained
Plain English explanation of SPF, DKIM, DMARC, and MTA-STS, with guidance on when to review email security settings.
Cloud Storage vs Backup. Why Sync Is Not Backup
Explains the difference between synchronisation and proper backup, how deletion and ransomware can propagate in cloud storage, and why independent versioned backup matters.
Email, Microsoft 365 and Collaboration Systems
Guides related to email platforms, Outlook behaviour, authentication policies, Microsoft 365 collaboration, shared documents, Teams, OneDrive and SharePoint.
Guides:
Email not working for your business. What to check first
A clear, non technical guide explaining why business email stops working and what to check before making changes. Helps identify whether the issue is local, account related, or system wide.
Outlook not sending emails but webmail works
Explains why Outlook can stop sending or receiving emails even when webmail works correctly, and how to recognise when the issue is local to one device rather than the email service itself.
Outlook calendar and contacts do not sync to iCloud
If Outlook calendar and contacts are not syncing with iCloud, this guide explains common causes, including error 0x800706ba, safe checks to try first, and when help is needed.
Printer or scanner cannot send email using Google Workspace
Explains why printers and scanners often stop sending email when using Google Workspace, following security changes. Outlines the available options at a high level and explains when assessment is needed, without step by step configuration.
Microsoft Teams issues for external users and guests
Explains common limitations affecting external users and guests in Microsoft Teams, including recordings and file access.
Solution to the Disappearing Bullet Points in Microsoft Outlook
Fixes an Outlook issue where second level or nested bullet points disappear after sending emails.
Excel Asking You to Save With a Different Name in OneDrive or SharePoint
Why Excel prompts you to save a shared file with a different name in OneDrive or SharePoint, and how to restore normal collaboration safely.
Why are shared documents not updating in SharePoint or OneDrive?
Explains why shared documents may not show another person’s changes when opened through SharePoint, OneDrive or the Office desktop apps. Covers AutoSave, encrypted files, read only behaviour, document protection, sensitivity labels and practical checks before changing the original file.
Security and Online Threats
Guides explaining security risks, scams, malware, account compromise, and practical account protection topics.
Guides:
Are passkeys and security keys the same thing?
This guide explains the difference between passkeys and security keys in plain language. Covers synced passkeys, hardware bound passkeys, YubiKeys, and why the terms are often confused.
How YubiKeys work and how to configure them in Intune and Entra ID
Explains what YubiKeys are, how they relate to passkeys, and how they are configured in Microsoft Intune and Microsoft Entra ID. Covers attestation, AAGUID restrictions, Conditional Access, rollout planning, and practical limitations to review before wider deployment.
Can money be taken from a locked phone using contactless payment?
Explains when contactless payments from a locked phone are possible, how NFC and Express Mode affect risk, and which settings are worth reviewing on Android and iPhone. Also outlines what physical shielding can and cannot do, so the topic is understood as part of wider layered security.
Fake CAPTCHA Malware on WordPress Websites Explained
This guide explains how fake CAPTCHA malware appears on compromised WordPress websites, how it attempts to trick visitors into running malicious commands, and what practical security controls reduce the risk of recurrence. It includes immediate containment steps and longer-term hardening measures based on real-world incident patterns.
WhatsApp security guide. How to protect your account and device
Explains practical steps to reduce the risk of account takeover, protect sensitive messages, and limit exposure if a phone is lost or stolen.
WhatsApp Verification Code Scam Explained
Explains why attackers request WhatsApp verification codes, how the scam works, and what steps to take if you receive or accidentally share a code.
How to Check if Someone Is Using WhatsApp Web on Your Account
Explains how to check whether WhatsApp Web or desktop sessions are connected to your account and how to safely log out of devices you do not recognise.
How to Check if Your WhatsApp Account Has Been Hacked
Explains the common signs that a WhatsApp account may have been compromised and how to confirm whether another device may be accessing your messages.
Stop People Adding You to WhatsApp Groups
Explains why people may add you to WhatsApp groups without permission and how to control group invitations using WhatsApp privacy settings.
Your Phone Number Was Registered With WhatsApp on a New Device
Explains why WhatsApp may report that your phone number has been registered on a new device, what situations normally trigger this message, and how to confirm whether your account remains secure.
How to check if a download is safe when everything looks legitimate
A practical guide using the recent fake 7-Zip installer case to explain what you can realistically check and how to reduce risk if detection lags.
Why trusted services can still be used in cyber attacks
Explains why email platforms, document links, cloud tools, browser extensions, supplier portals and website services can still be used in cyber attacks. Outlines how trust is abused and what small organisations can review across accounts, permissions, data movement and recovery.
How do software supply chain attacks happen?
Explains how software supply chain attacks can happen when trusted tools, plugins, developer workflows or third party services are compromised. Covers developer tools, security tools, tokens, API keys, supplier access and practical steps for reducing unmanaged trust.
Can websites in Google search results still be dangerous?
Explains how unsafe or compromised websites can still appear in search results, how they behave once opened, and what to check before interacting with unfamiliar pages.
How to reduce the risk from unsafe browser extensions
Explains how browser extensions introduce risk, how permissions work in practice, and how to review and manage extensions safely over time.
Explains why PDF files can still be used in real attacks, how trusted document workflows are sometimes abused, and what protection layers help reduce risk. Also outlines the limits of PDF hardening so the topic is understood as part of wider security, not as a single setting or permanent checklist.
Websites, WordPress and Online Services
Guides covering website security, hosting behaviour, and web infrastructure.
Guides:
WordPress Hardening for Small Organisations
Explains the practical security controls that help reduce risk on WordPress websites, including correct file permissions, access controls, configuration settings, and monitoring. Outlines what to verify in a typical hosting environment and how these measures support ongoing website stability.
Wordfence Security Settings Review
Explains how to review essential Wordfence security settings in a structured way. Covers firewall configuration, login protection, file integrity monitoring, and alert discipline within a layered security approach.
WordPress security headers explained. How to add them safely
Learn how browser enforced security headers work, how to implement them safely in WordPress, and how to verify they are active using Chrome DevTools.
sprites core SVG 404 error in WordPress and Divi
Explains why a sprites core SVG 404 error may appear in browser consoles or audit reports on WordPress and Divi sites, what it means in practice, and when action is required.
Why a page is missing from the Yoast sitemap
Explains why a published WordPress page can be missing from the Yoast XML sitemap, and the canonical URL detail that is commonly overlooked.
Bing reports HTTP 400–499 errors on my website
Why Bing can report HTTP 400–499 errors even when a site works normally, how Cloudflare settings like Browser Integrity Check can affect scans, and how to verify results safely.
Networks, Internet Connectivity and Infrastructure
Guides explaining how networks and internet infrastructure affect systems.
Guides:
Laptop connected to WiFi but no internet
Explains why a laptop can show a WiFi connection while internet access is unavailable, and how to understand whether the problem is local, network related, or external.
Understanding internet access in offices, hotels, and public places
A plain-English guide explaining office internet, mobile hotspots, public Wi-Fi risks, and how to connect devices more safely.
Fixing Paramount Plus playback issues when using NextDNS
If Paramount Plus does not work on an LG TV, Sky TV box, or web browser while using NextDNS, this guide explains why and how to restore streaming without disabling DNS protection.
ChatGPT not working in Firefox. What to check and what helps
Why ChatGPT may stop working in Firefox, common symptoms, and realistic workarounds without weakening security.
How to access CCTV from a computer or web browser
If you can view your CCTV on your phone but not on a computer, this guide explains why that happens and what access options are realistically available today.
Computers, Devices and Software
Guides explaining common issues affecting computers, phones, routers, software, and everyday device behaviour. These include Windows upgrade limitations, OneDrive folder behaviour, device migration, system performance, and realistic options when devices or software reach the end of their supported lifecycle.
Guides:
Can I use my own router with my ISP connection?
Explains when a third party router can replace an ISP router, when bridge mode or modem only mode is the cleaner design, and when DMZ may be the next best option. Also outlines what common terms such as ISP, private IP address, public IP address, static IP address, and dynamic IP address mean so the design choices are easier to understand.
Windows 10 is no longer supported. What are your options?
Explains what Windows 10 end of support means, why some devices cannot upgrade to Windows 11, and what supported options exist.
Computer running slow. What actually helps
Explains the most common reasons a computer becomes slow, what checks are worth doing first, and what usually helps in practice without assuming the device needs to be replaced.
How to move to a new Android phone without losing data
Explains how to move to a new Android phone without losing important data. Covers storage checks, cable transfer, SMS migration issues, WhatsApp backup and restore, Google Discover on Samsung phones, and what to review before converting from a physical SIM to an eSIM.
Why can’t I move my Documents folder out of OneDrive?
Explains why Windows may stop Documents, Pictures or Desktop from moving out of OneDrive or returning to their default folders. Covers the access denied folder redirection error, what to check before changing folder paths, and why registry correction should only be treated as an advanced recovery step.
Reviewing a Technical Issue
If a technical issue appears to affect shared systems, email flow, cloud platforms, website behaviour, or operational continuity, you can provide details so we can review whether structured support is required.
